Self-protected network Cisco
Evgenie Rudometov
According to the last researches, safety is the most serious problem which users of computers have faced. Continuously varying threats of safety as with external and c an inside of the business oriented network can bring chaos in business operations, negatively effecting profitableness. Thus before private users and heads of small enterprises, there are same problems of safety, as before a manual of the big companies. It both virus attacks, and espionage programs, and the employees stealing the confidential information. A difference only that their financial and manpower resources are often non-comparable. Nevertheless, in approaches to a safety problem is and much in common. Really, many of the named categories use diverse solutions which have appeared as a result of long-term unsystematic acquisition and installation of so-called dot solutions. Anti-virus programs, and various management systems concern them and monitoring both internetwork screens, and systems of preventing of intrusions (IDS), both. A problem of diversity of the resources used by end users, that fact complicates also, that they are made by the different companies and realised by different corporations.
Possibly, there is no necessity to prove, that absence of a system approach inevitably generates chaos. It leads to idle time or to ineffective operation of many of used components. And as result - to a low level of protection of the information. Thus to predict a degree of inaccessibility in case of attacks of malefactors it is simply impossible. The given circumstance results or in the overestimated waitings of the users blindly trusting to diversity of used resources, or on the contrary - to their underestimation. Both that, and another is fraught with troubles.
The problem of the diverse equipment consists and that different arrangements are controlled by different systems. And, as is known, diverse arrangements extremely difficultly effectively to control, if at all it is possible. It is linked by that it is necessary to gather data from each system, to compare these data, and also manually to watch operation of each of hardware arrangements or program components. All it is very difficult and expensive, especially in the conditions of limited financial and manpower resources that is characteristic and for private users, and for the small-scale business companies.
Responding to requirements of the market, company Cisco which is one of leaders of network processing techniques, offers the various solutions routed on protection of the information. The presentation of the newest products (the Photo 1), attempts of unauthorized access providing effective reflexion to the confidential information has been devoted the given subject led in Moscow on February, 14th.
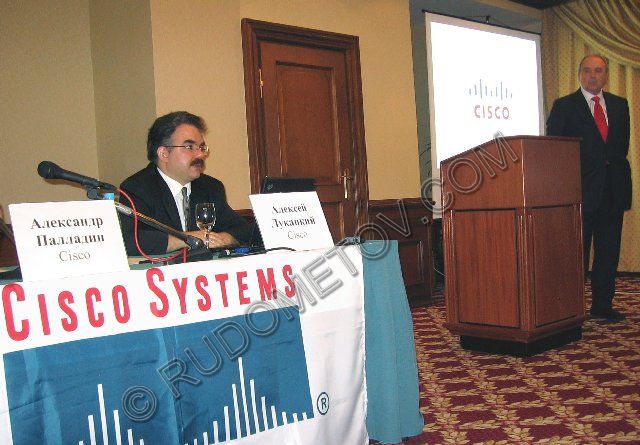
Photo 1. Presentation of products Cisco
Protection system basis is "self-protected network Cisco" (Cisco Self-Defending Network). It integrates into uniform system all resources of safety, including internetwork screens, systems of preventing of intrusions and anti-virus programs.
For "brain" of the centralised infrastructure of safety the system of monitoring and reaction to threats CS-MARS (Cisco Security Monitoring, Analysis, and Response System) is.
The important component of self-protected network Cisco the program of safety Cisco Security Agent (CSA) which works on transportable computers, desktop computers and servers is considered. Unlike the traditional anti-virus scanners comparing program codes with signatures of known viruses, CSA parses behaviour of users and arrangements, detects anomalies and locks possible attacks, including what are "skipped" by the standard anti-virus scanner. The main feature and value CSA consists that this solution locks threats in the germ. Threats are locked during the moment when anti-virus programs only start to recognise type of an unknown virus and to build the new signature.
Besides, the CSA component gives a number of possibilities of handle of system hardware. In particular possibility of disconnecting of some tools through which it is possible to steal the confidential information is provided.
And in complex system it is offered to use built in systems of enciphering and the decoding, working on different levels.
All components provide protection high levels, as from external attempts of unauthorized access, and external. Thus implementators of system assert, that all is made possible not to limit users and to provide a functionality maximum level. It in particular is reached by an effective utilisation, both system possibilities of used OS, and specially developed units. Many if not to tell - the majority, of protection frames work in an automode, not distracting on trifles of the system administrator and users. It is necessary to add, that many components work on the adaptive algorithms, allowing to consider the stored experience linked to reflexion of attacks and overcoming of hardware-software glitches. All it essentially raises value of the made operation.
Certainly, frames of short article do not allow to estimate in details all components of a protection system, and hardly it is expedient. Self-protected network Cisco is the long-term strategy the company on protection of business processes by revealing, preventing and adapting to external and internal threats. It continuously develops and finds new functionality.
 English
English Russian
Russian German
German